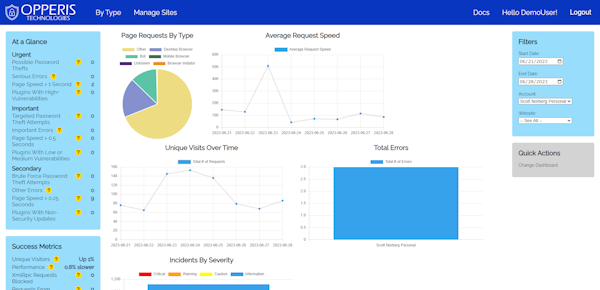
All-In-One Monitoring
We offer an all-in-one product that monitors your app in production. We offer monitoring over these broad categories:
- Performance
- Traffic
- Errors
- Security
In addition to monitoring, we also offer some security protections, such as automatic configuration and blocking known-bad traffic.
Browse our features below to learn more!
 Website Performance
Website Performance
| Feature | Availability |
|---|---|
| Quick and easy configuration ? | |
| Track performance by page ? | |
| See performance changes over time ? | |
| Compare speed of your websites ? | |
| Monitor hook execution speed ? | |
| Notifications for slow pages ? | |
| Site uptime monitoring ? | |
| Comparison to other sites ? |
 Incoming Traffic Analysis
Incoming Traffic Analysis
| Feature | Availability |
|---|---|
| Quick and easy configuration ? | |
| See traffic by type (desktop, mobile, bot, etc.) ? | |
| See traffic by software (Chrome, Firefox, etc.) ? | |
| Compare traffic between your websites ? | |
| View traffic that Google Analytics misses ? | |
| Advanced header analysis ? | |
| Location analysis ? | |
| Comparison to other sites ? |
 Runtime Error Detection
Runtime Error Detection
| Feature | Availability |
|---|---|
| Quick and easy configuration ? | |
| Track errors in your website ? | |
| See who experienced the error ? | |
| See which of your websites cause the most errors ? | |
| Discover which theme or plugin caused the error ? | |
| Notifications for errors ? | |
| AI-driven remediation advice ? |
 Vulnerability Tracking
Vulnerability Tracking
| Feature | Availability |
|---|---|
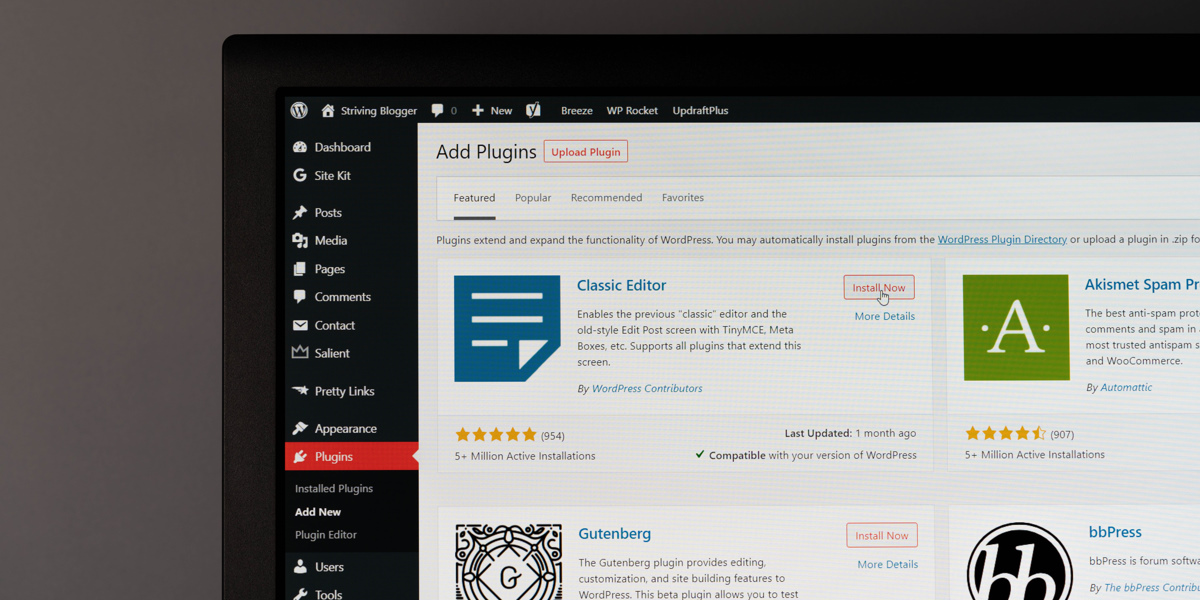
| Quick and easy configuration ? | |
| Detect missing headers ? | |
| Plugin and Theme Monitoring ? | |
| Schedule External Scans ? |
 Security Incident Detection
Security Incident Detection
| Feature | Availability |
|---|---|
| Quick and easy configuration ? | |
| See data validation issues ? | |
| Discover stolen password usage ? | |
| Detect malicious visitors ? | |
| Detect breached passwords ? | |
| File Upload Checking ? |
 Security Protection
Security Protection
| Feature | Availability |
|---|---|
| Quick and easy configuration ? | |
| Automatically add security headers ? | |
| Automatically block malicious visitors ? | |
| Block Spam Messages ? |
Looking for other features? Please contact us! We may be able to include it in our product.
Further Reading
Read about how attackers have abused our simulated WordPress endpoints on our non-WordPress sites.

Cryptography is almost impossible to get right. Read about common mistakes, and what you should do instead.

Logging for security is not at all like logging for debugging. Click here to read why.
Get started today!